Hi!
Today we are going to review the hunter.io service Do you know it? It consists on a web service which lets you search for email accounts published on Internet through indexed results of search engines.
In addition, it lets to either search a professional email account or to verify an email account.
By doing a simple search by the name of a company such as the own hunter.io, the application returns the following results:
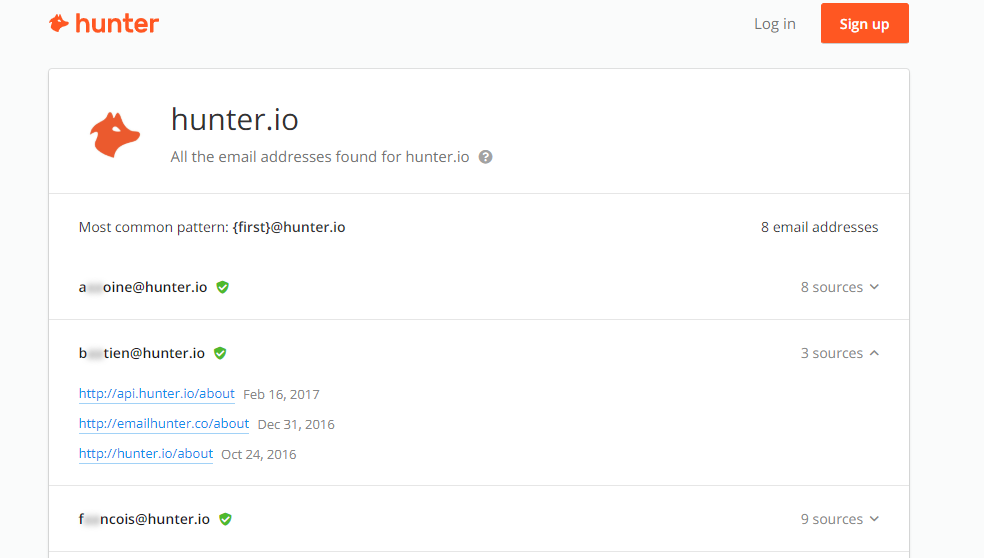
As you can see in the previous evidence, the results are partially obfuscated. If you want to see them properly, you should register in the application and create an account:
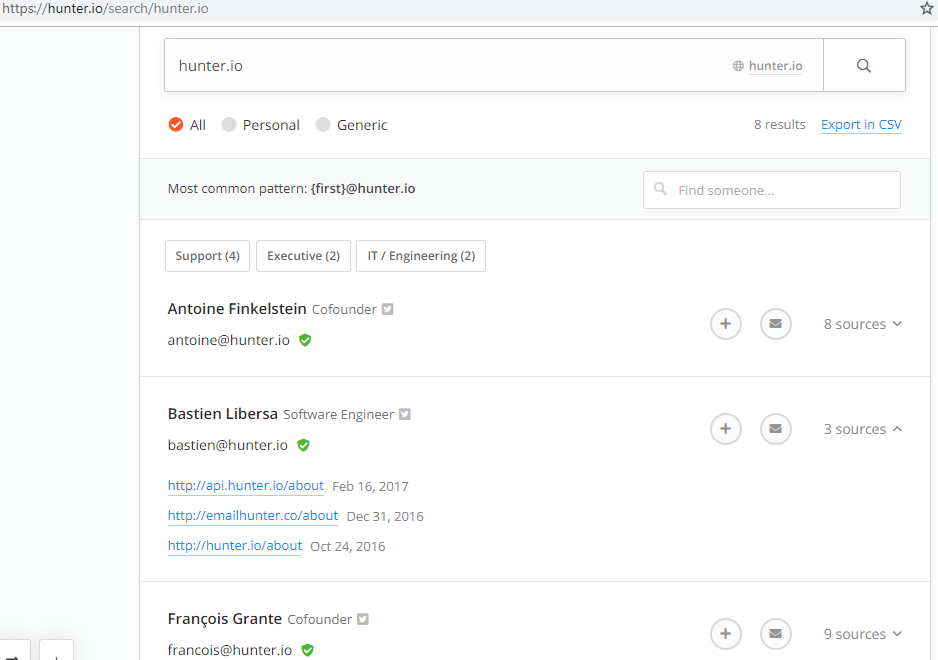
In addition, for each result hunter.io shows the sources where the results are found.
After understanding the work of the service, let’s to see the interesting goal: the automation of this. For this, APIs are welcome and hunter.io has a free API, but of course it is limited for customers to spend money on the premium API. All documentaton about the API is available here: https://hunter.io/api/docs
To understand how it works from my point of view the best thing is to take an example, see how the information comes and take the one that interests us according to our needs. To do this, we shall use the example that comes in the documentation:
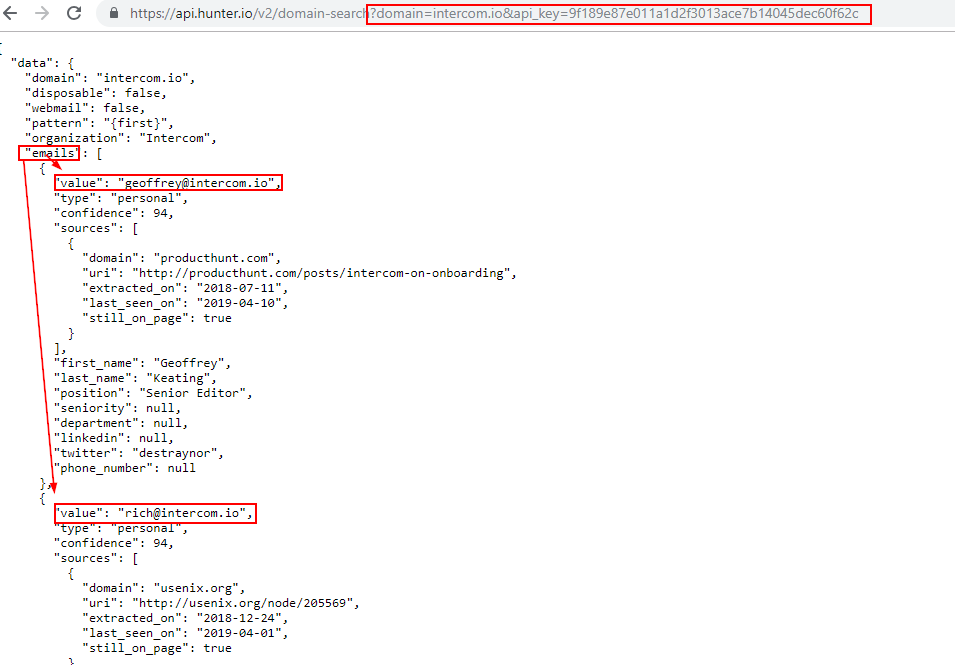
As you can see, being a REST API, it is based on a GET HTTP request where the domain and our API_key are used. Once I understood how the API works, I created a simple script that automates this process by taking the results of the emails after entering the domain you want to search. You can find it in my github: https://github.com/n4xh4ck5/pyhunter
The script is developed in python 2 and 3 (thanks to @Guille_hartek for collaborating with the translation from python2 to python3, you know, changing the print functions xd)
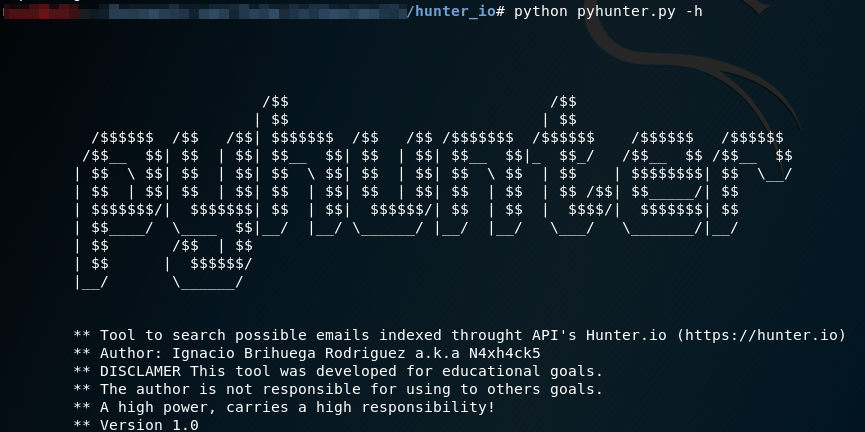
The script takes the domain as a parameter:

It returns the results by screen, as well as exporting an excel file with the name «hunter.xlsx»
I have followed the hunter.io service for a long time because I had to use it to search possible emails indexed to prepare a phishing campaing (for work). On the way in the AVE train to OSINT City in the last weekend, I could finally play with it.
Probably there are many better scripts in github than mine, but I looked forward to play with it 😉
I am hope you all find this post useful!
See you in the next CON.
Kind regards.
N4xh4ck5.
«The best defense is a good attack.»