Hi Minions:
Serve yourself the ☕️first coffee☕️, that this is going to be a bit long, and I still don’t even know how to focus this article 😅
Why is it difficult for me to start this article? Because I want to talk you about the Windows Registry. How to use some tools to do a Windows Registry Analysis.
Analyze the Windows Registry is an imprescidible and fundamental step in any case. Not surprisingly many forensic tools base their operation on data extraction from certain registry keys. From Registry we can extract unique information that wont be found elsewhere.
And this is not easy, unless you know the Registry perfectly. In fact, I will not do any analysis of any particular case. I will just explain how to use what we are going to see, and see some example of what kind of information can be extracted.
I think it’s very difficult to understand its operation. That it takes a lot of study time to understand it.
Maybe, I should start by defining what is the Windows Registry.
And what better way to do it than from the Microsoft site itself. On a page entitled «Windows registry information for advanced users» wich us refers to the «Microsoft® Computer Dictionary 5th ed. Edition«, which tells us, literally
«A central hierarchical database used in Microsoft Windows 98, Windows CE, Windows NT, and Windows 2000 used to store information that is necessary to configure the system for one or more users, applications and hardware devices.
The Registry contains information that Windows continually references during operation, such as profiles for each user, the applications installed on the computer and the types of documents that each can create, property sheet settings for folders and application icons, what hardware exists on the system, and the ports that are being used.
The Registry replaces most of the text-based .ini files that are used in Windows 3.x and MS-DOS configuration files, such as the Autoexec.bat and Config.sys. Although the Registry is common to several Windows operating systems, there are some differences among them.»
The Windows Registry, despite being a hierarchical database, is divided in files, called hive. Some hives are volatile and are not stored on the disk and not all are loaded at the same time.
As a curiosity, why hive? Because one of the original Windows NT developers hated bees. So the developer, who was responsible for the registry, put as many references to bees as he could.
And, what is a ‘hive’? This time, we go to another page of the site of Microsoft, entitled «Registry Hives«, and tells us that
«A hive is a logical group of keys, subkeys, and values in the registry that has a set of supporting files containing backups of its data.
Each time a new user logs on to a computer, a new hive is created for that user with a separate file for the user profile.
…
A user’s hive contains specific registry information pertaining to the user’s application settings, desktop, environment, network connections, and printers.»
With all this you can already have an idea of the amount of information that handles the Windows Registry.
I’ve always thought that the Registry is the heart of Windows. Any incorrect manipulation of it affects the System in a critical way. I would even say that almost any action that occurs in the system, is recorded on it.
What types of registry files are on a Windows system? What is its location?
C:\Documents and Setting\User Profile\NTUSER.DAT o C: \Users\User Profile\NTUSER.DAT
C:\Windows\System32\config\DEFAULT
C:\Windows\System32\config\SAM
C:\Windows\System32\config\SECURITY
C:\Windows\System32\config\SOFTWARE
C:\Windows\System32\config\SYSTEM
And, what are the volatile Hives?
HKEY_LOCAL_MACHINE\Hardware
HKEY_LOCAL_MACHINE\System\Clone
Are these all records that are on a Windows system? There is more? Yes, there are more. Since the Windows Vista versions, two more Registries have been included.
C:\Windows\System32\config\COMPONENTS
C:\Users\username\AppData\Local\Microsoft\Windows\UsrClass.dat
Already? No. From Windows 8 have been included another four more.
C:\Windows\AppCompat\Programs\Amcache.hve
C:\Windows\System32\config\ELAM
C:\Windows\System32\config\BBI
C:\Windows\System32\config\DRIVERS
And, of course, it is highly recommended to know its structure. So I will not speak more than registry. You have a lot of information available on the Net, starting with the official Microsoft site, «About the Registry«.
There is also quite interesting information about the Windows Registry in ForensicWiki.
Seen, very, very, very superficially, what is the Windows Registry, let’s see how we can analyze it, make readable information it.
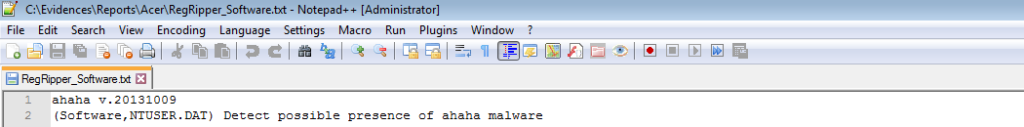
For this, we will use a tool par excellence in this field. RegRipper.
RegRipper is an open source forensics software application developed by Harlan Carvey. It is written in Perl, and is a tool used for extracting data from the Windows Registry. It also has a separate Windows executable, «compiled», of the script using ‘Perl2Exe‘. So it is possible to use it in both Linux and Windows environments. No installation required, which means it is portable.
Who’s Harlan Carvey? When we talk about Harlan Carvey, we speak of one of the biggest specialists in the registry of Windows, (that I know, in addition to others that I hope to be able to speak later). Not in vain is, among other things, author of the blog Windows Incident Response, (a blog obligated reading if you are interested in this matter), dedicated to the huge information on DFIR matter on Windows systems. He is also the author of numerous books on this subject, of which I will highlight «Windows Registry Forensics: Advanced Digital Forensic Analysis of the Windows Registry«, «Windows Forensic Analysis DVD Toolkit«, and «Digital Forensics with Open Source Tools«, written next to Cory Altheide.
Our friend @fpalenzuela, from the Sysadmin Trainee Blog already introduced us to the use of RegRipper in a couple of entries. I’m going to try to talk with another approach.
I usually use it in my Linux lab, but this time we’re going to use it on a Windows lab.
After mounting the image of the System that we want to analyze, always as read only, or after extracting the files from the Registry and copying them to our laboratory … We started.
As always, and first of all, the first thing we have to do is to download the RegRipper tool from its official site in Github.
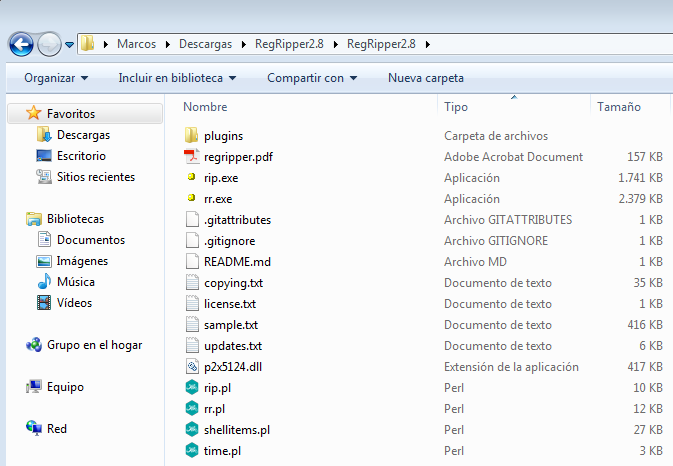
After downloading and unzipping it, these files are presented to us.
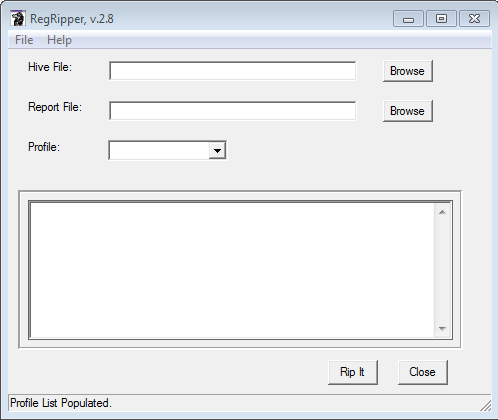
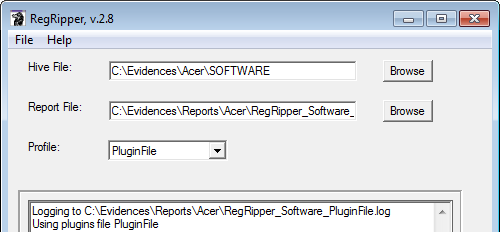
The ‘traditional’ way to run it is through the executable ‘rr.exe’, which shows us this screen after its opening.
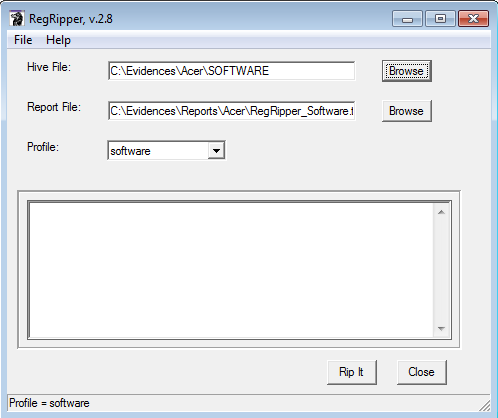
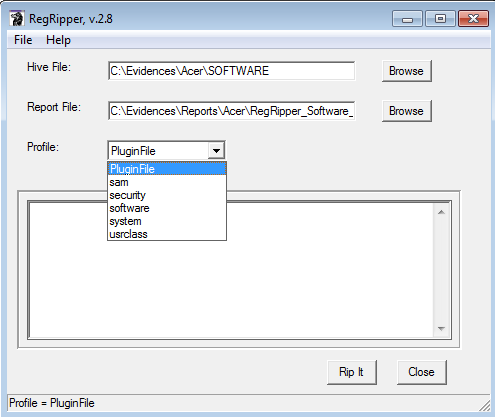
Once opened, we just have to indicate, using the ‘Browse’ buttons, the registry file that we want to parse and the name of the report we want to generate. We also select, by using the drop-down, the profile we want to load, (a profile for each file in the Registry), and give the ‘Rip It’ button.
It can work on a total of 346 plugins in total, to date.
☕️Second coffee☕️
Once it is finished, we will be able to see, at the top of your text box, the path where the ‘.log’ file and the profile that was used to perform data extraction have been generated.
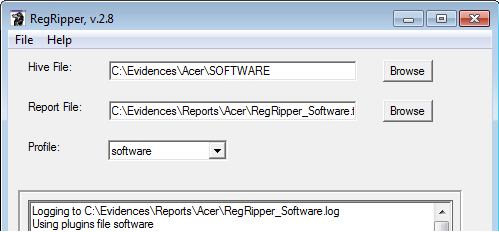
We will also be able to see, at the end of the text box, if there were any plugins with errors.
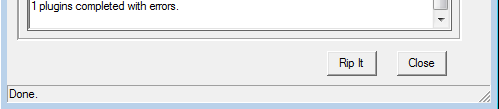
If we go to the route that we indicated above to generate the report files, we will note that two files have been generated.
One is ‘.log’ and another is ‘.txt’.
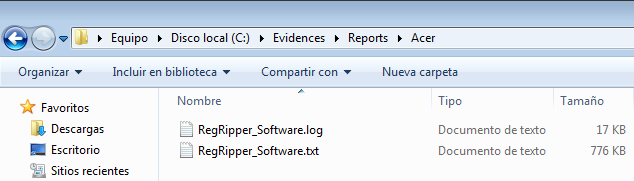
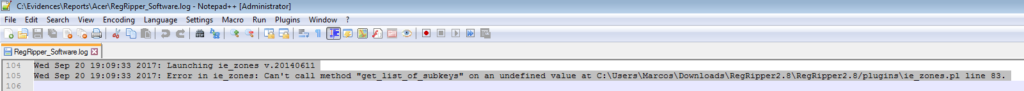
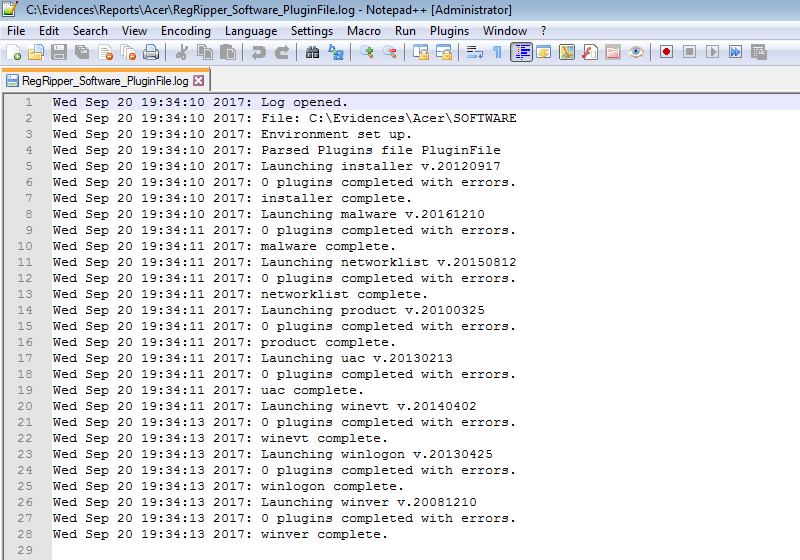
The ‘.log’ file contains information about the execution of the program. And its reading is very interesting because we can see if the plugins have thrown some kind of error.
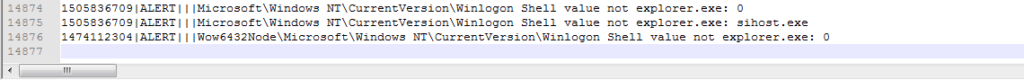
The ‘.txt’ file contains all the information that has been extracted from the Windows Registry file that we have parsed. All of it. In this example it have used 110 plugins that can work on the ‘SOFTWARE’ registry file.
We can see that, in this case, it has 14876 lines. And the size of the generated file can be smaller or larger than in this example, because it depends on the use of the machine, among other things.
We all know that
The tools do NOT perform the analysis themselves. The tools help, but the work does, for the moment, the analyst.
And, given the huge amount of information that can be contained in a registry file, it can take a long time to study this report. Even more so if you are not looking for anything in particular.
For this reason, Harlan Carvey also wrote a tool called ‘Plugin Browser‘, which allows you to manage the plugins that RegRipper uses through a graphical user interface. With this tool you can create a profile, totally according to our needs.
It is very intuitive to use. This tool is available on your official Google Code site.
We download the file ‘wfa3e.zip’ (Windows Forensic Analysis toolkit 3rd edition), which is the material associated with that book.
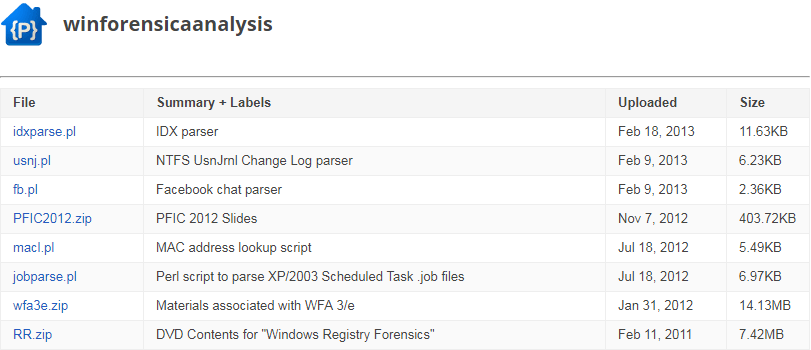
We proceed to its decompression and it will present us these files, inside the folder ‘ch5 \ RegRipper’.
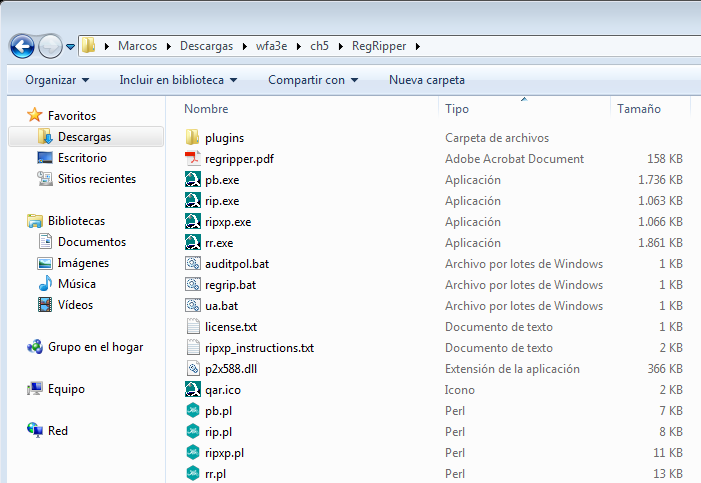
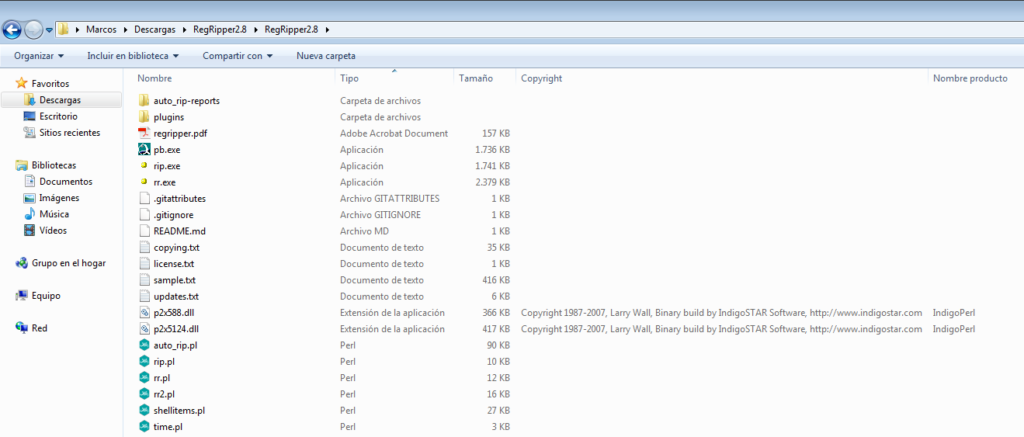
Once we are in that location, we proceed to copy the files ‘pb.exe’ and ‘p2x588.dll’ to the folder where we have the version of RegRipper that we have downloaded before.
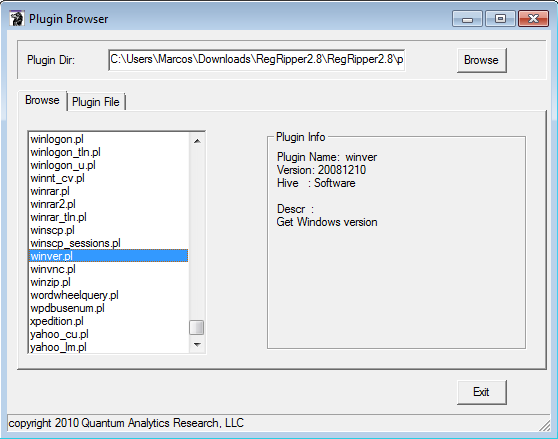
We execute the file ‘pb.exe’ and this window is presented to us.
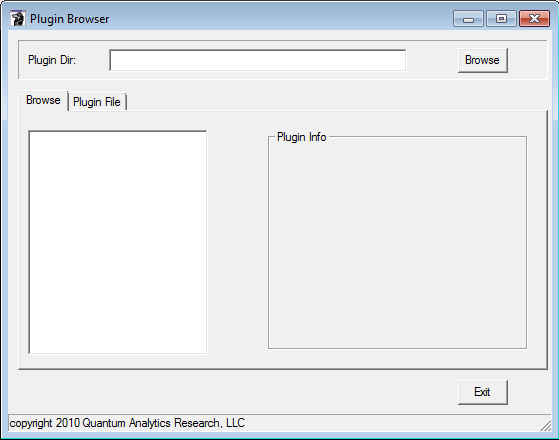
And, as I said earlier, it has a very simple use. Just use the ‘Browse’ button to open a window where we will choose the folder containing the RegRipper plugins. After selecting it, we use the ‘OK’ button.
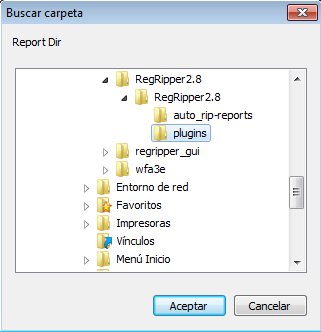
All the plugins that are in that folder will be loaded in the text box on the left. If we select one, It will show us information related to that plugin, containing the name, version, the hive it is able to work on and a brief description of what it does.
If we move to the ‘Plugin File’ tab, we can select as many as we want and, using the ‘>>’ button, are added to the text box on the right. These will be the plugins that will use our custom profile, which we can save with the ‘Save’ button.
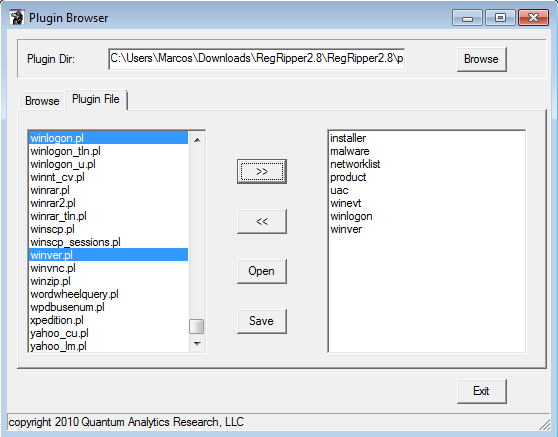
Assigning the name we want.
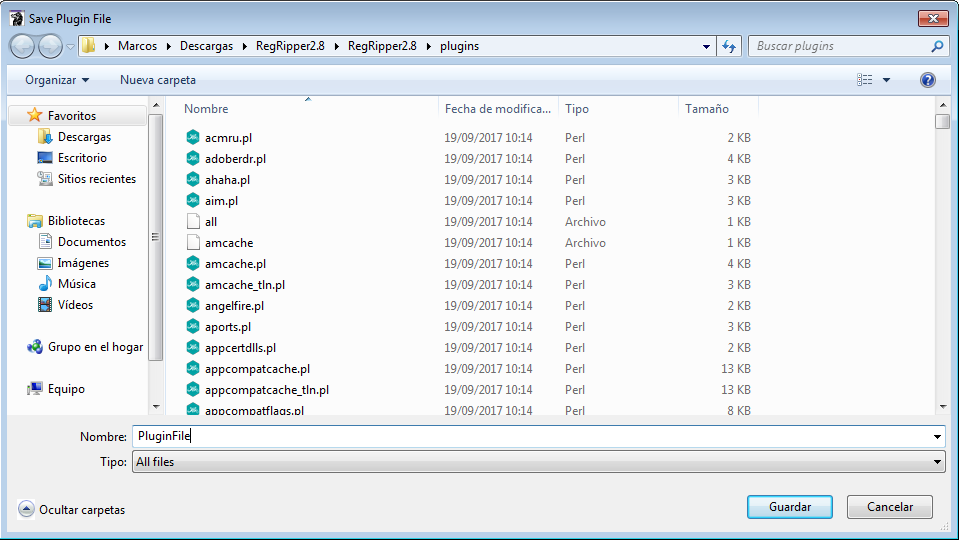
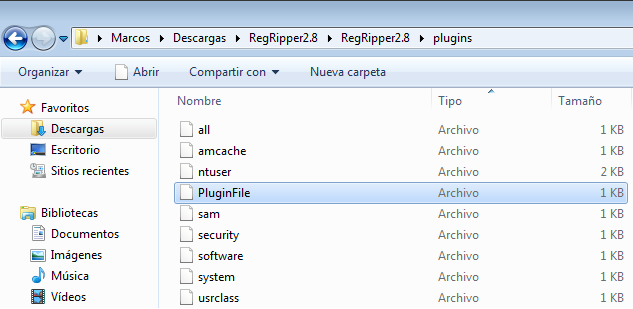
We can see the file inside the folder of RegRipper plugins.
‘Plugin Browser’ also allows the editing of these profile files. To do this, we use the ‘Open’ button
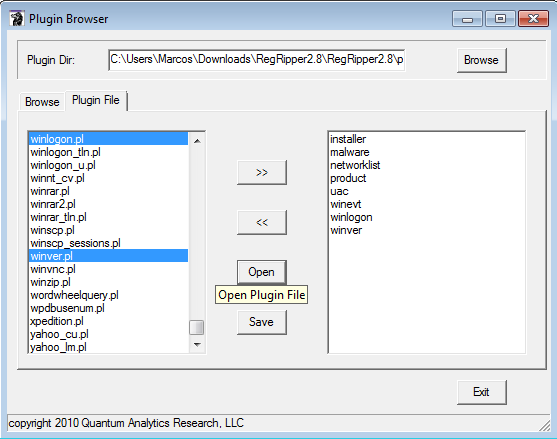
To open the profile file that we want to edit and, after opening it
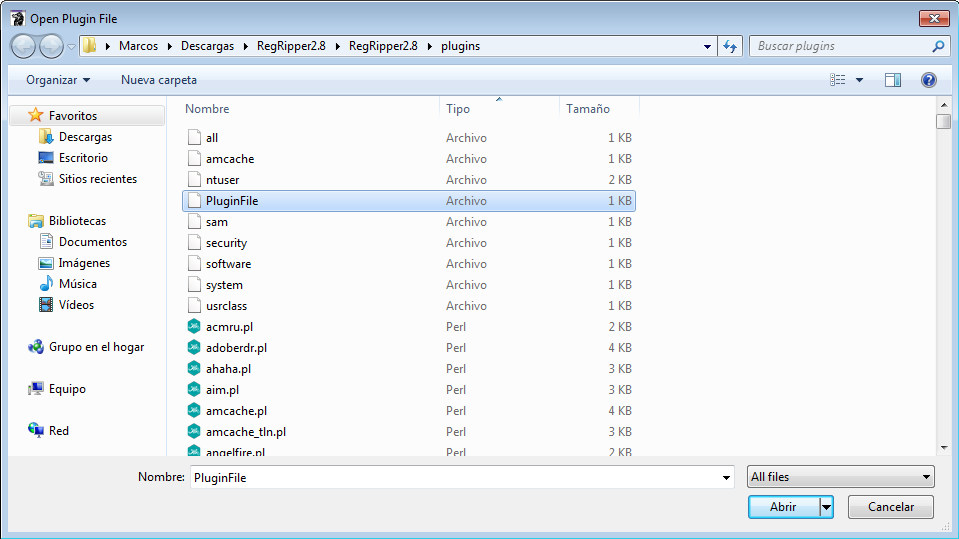
It will present us your information in the text box on the right.
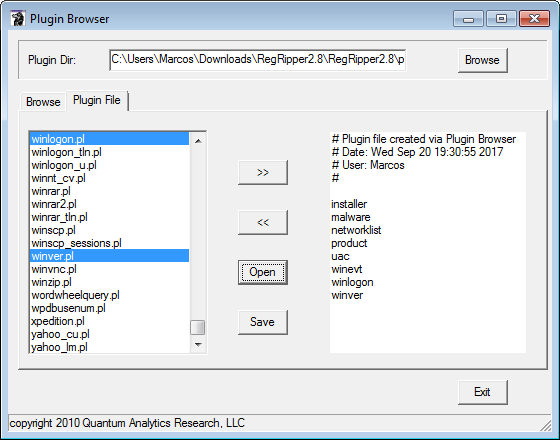
Once the profile is customized, with the plugins we want to use, we can reopen ‘rr.exe’ and, on this occasion, in the drop-down list, we will be able to see and select it. And after running it with ‘Rip It’
☕️Third coffee☕️
We can see, as before, the route where reports will be generated with the profile used
And if there have been errors.
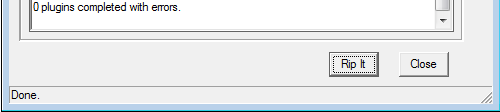
If we open the generated ‘.log’ report, we will be able to see what Registry files have been used, the profile used and the plugins used.
In this way a more precise result is obtained, which always depends on the case that we have to analyze.
In this example we can see how the number of lines in the generated ‘.txt’ report has been drastically reduced.
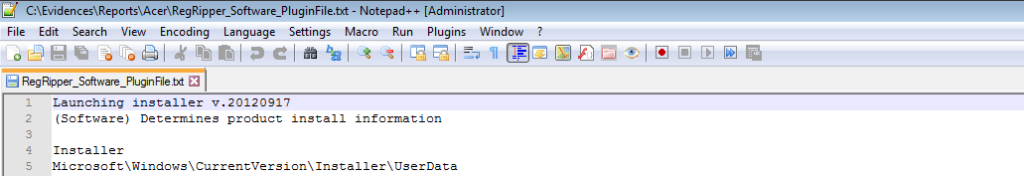
We have gone from 14876 lines to 4558.
And, what information can we get? For example, and for starters, the Operating System with the installation date.
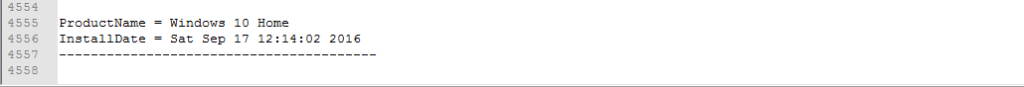
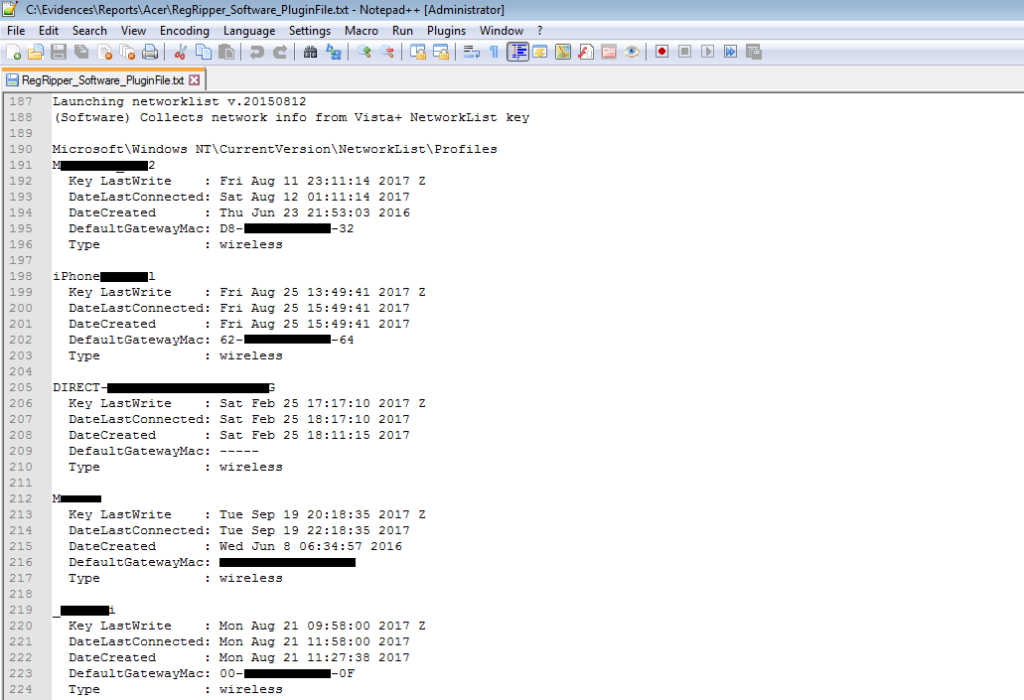
Or information on the networks to which the System has been connected, which includes, in addition to the network name and the date of last connection, the MAC address of the access point, which can be geolocated on a map using, for example, the online service of https://wigle.net/.
We can also see the software that is installed in the System
![]()
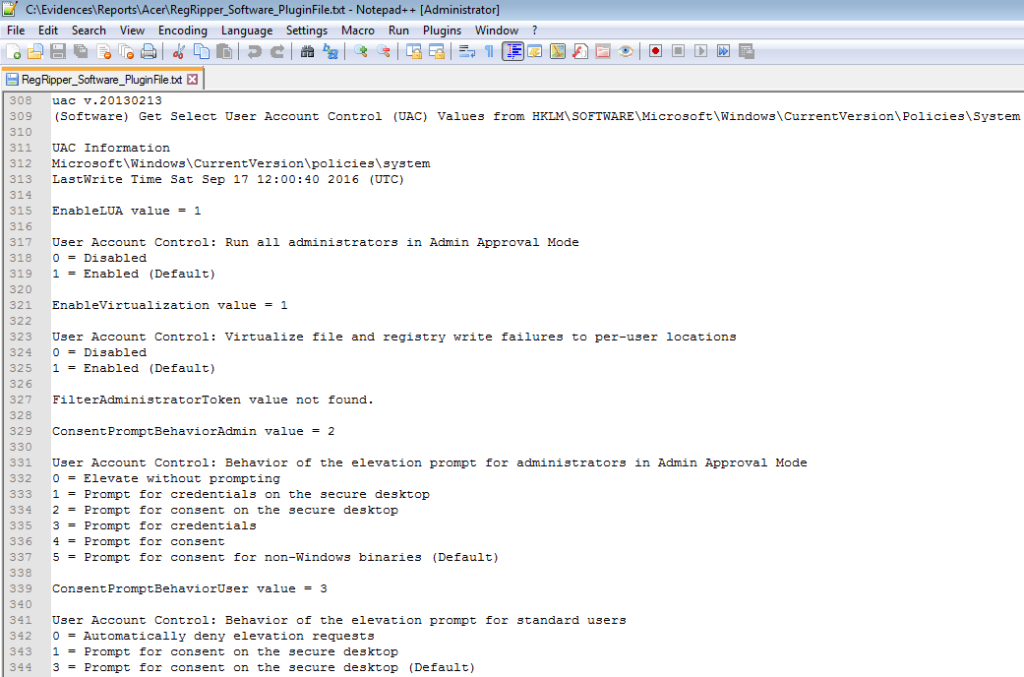
Or the UAC configuration information, (User Account Control), which I consider very important.
All right. We have used RegRipper with a complete profile and a custom profile, to obtain a more accurate result in our analysis. But let’s say that we want to use only one plugin. If we have to generate a profile to use only one plugin …
RegRipper allows you to use only one plugin to parse the registry information.
For this we go first to the ActiveState site because we are going to install ActivePerl.
We download the Windows version
And we proceed to install it, just like any other software.

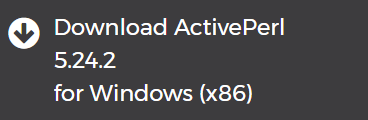
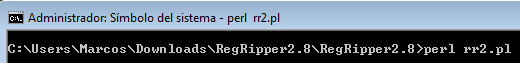
Now, we execute the Symbol of the system and we write
perl -h
And so easy we have installed Perl in our Windows System.
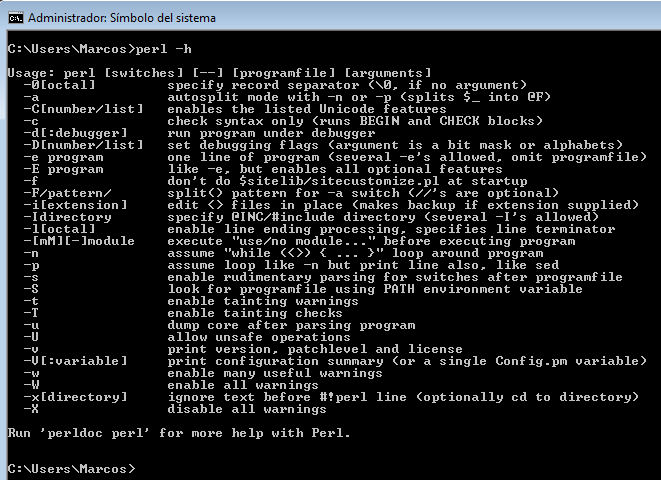
Now we go to the directory of RegRipper
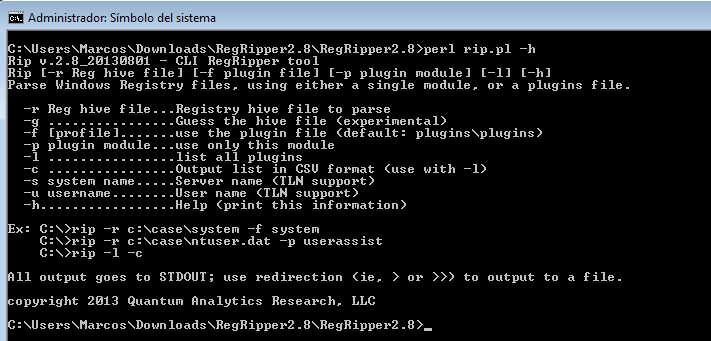
And we invoke the help of RegRipper, through
perl rip.pl -h
As we can see, its use is very simple even by command line. The program is invoked, you specify the Registry that you want to parse and you are specify the profile or a particular plugin. It can export the results to a file.
We can see all available plugins within their corresponding folder
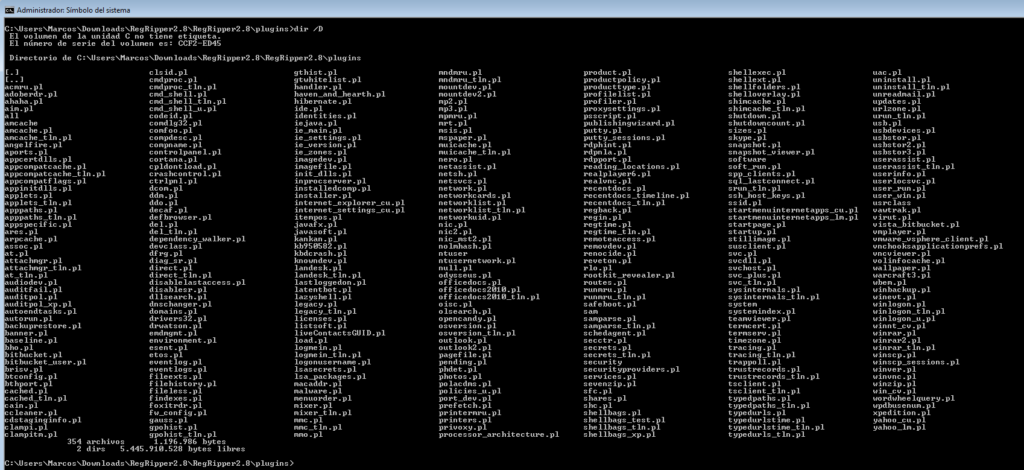
And we can list them through
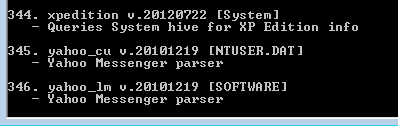
perl rip.pl -l | more

To see them in a slightly more detailed way.
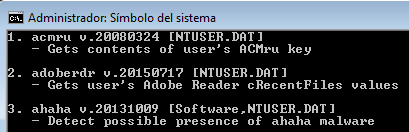
To date, 346 plugins are available.
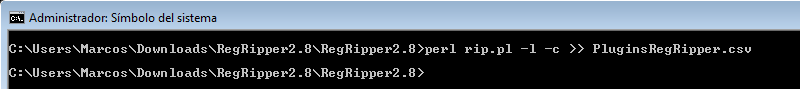
And we can also export the list of available plugins to a ‘.csv’ file to be able to have it as a reference, through
perl rip.pl -l -c >> PluginsRegRipper.csv
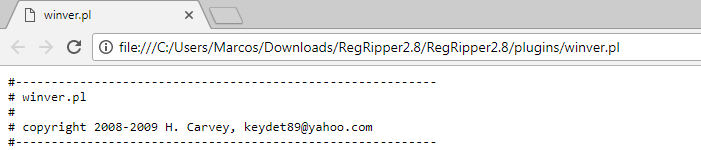
If we open a plugin to see its content, we can see that there are some that do not contain information about what it does
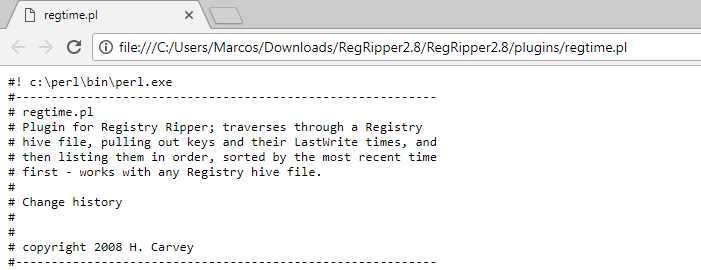
And others who do have it, very well detailed.
Well, I deviated from the subject. How does it work from the System Token? For example as well
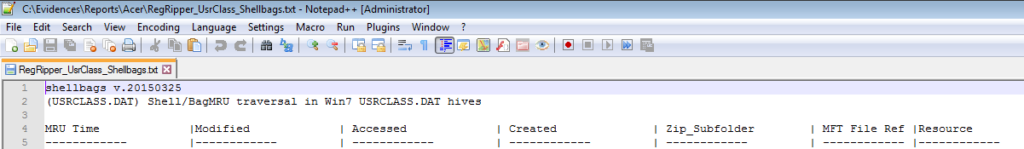
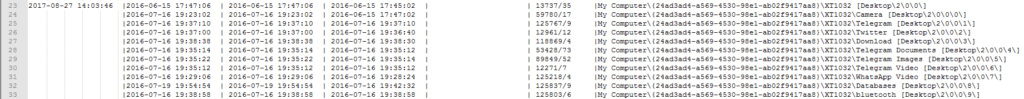
perl rip.pl -r C:\Evidences\Acer\UsrClass.dat -p shellbags >> C:\Evidences\Reports\Acer\RegRipper_UsrClass_Shellbags.txt
☕️Fourth coffee☕️

What have we got using the ‘Shellbags‘ plugin? We have extracted from the Registry keys details about the folders that have been viewed, with their corresponding time stamps.
This way of working is not bad at all, through the command line. It is very flexible. In fact, it is the one I usually use in my linux lab.
But we can still mold the tool to our needs.
To do this, Corey Harrell wrote a tool called ‘Auto_Rip’, which explains very well in his blog, Journey Into Incident Response, and that focused to use it with RegRipper, divided into categories. ‘Auto_Rip’ automates the execution of RegRipper plug-ins, according to a selected category, increasing the speed of data extraction from the Registry.
We can download ‘Auto_Rip’ from your official site in Google Drive.
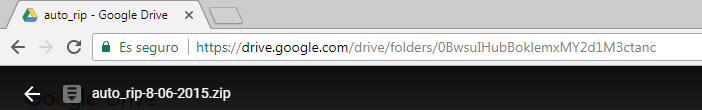
After decompressing these files are presented to us, which we copy in the same directory where we have RegRipper hosted.
![]()
We ask for help, to see what it offers us, through
perl auto_rip.pl
We can see the parameters that it offers. It is very simple to use.
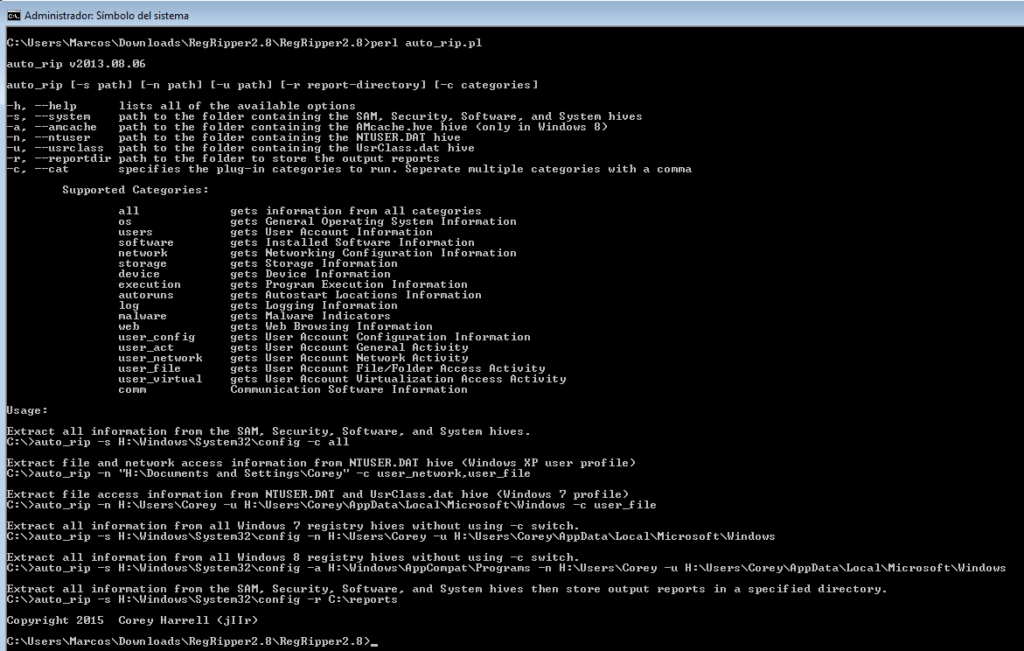
We can select one or more files from the Registry and tell it some categories …
perl auto_rip.pl -s C:\Evidences\Acer -s C:\Evidences\Acer -n C:\Evidences\Acer -u C:\Evidences\Acer -c network,comm,web -r C:\Evidences\Reports\
☕️Fifth coffee☕️
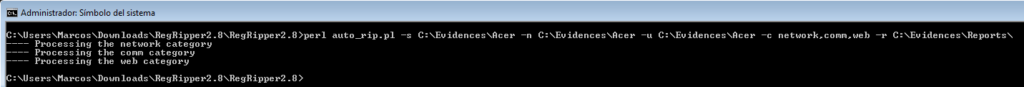
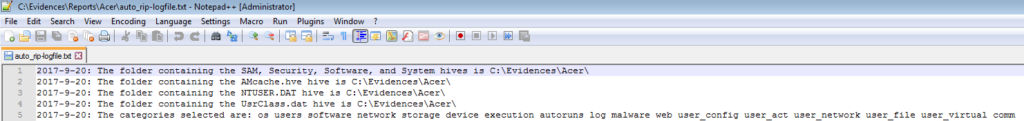
And it will generate, firstly, a file ‘.log’ that we will consult to see what registry keys we have analyzed and what categories we have used.
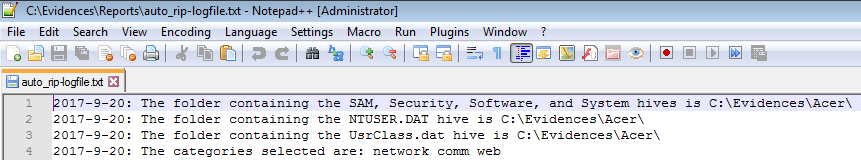
It will inform us properly of the errors that have occurred.
![]()
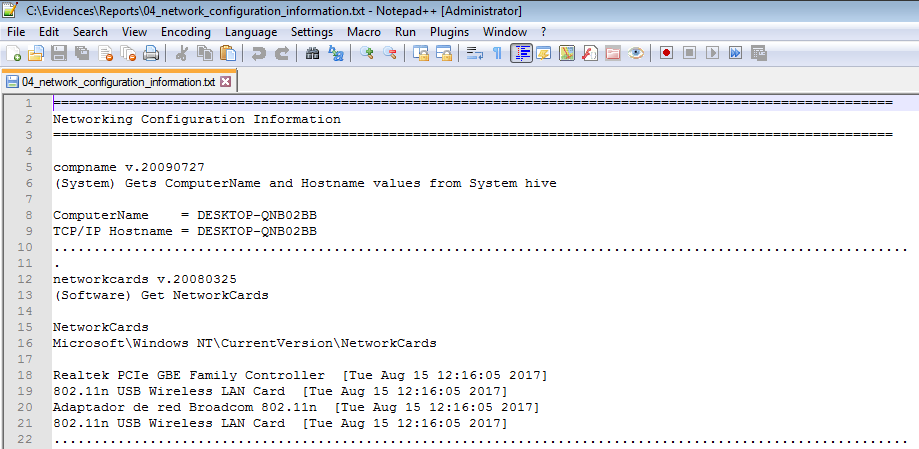
We can extract, for example, the name of the equipment and the network cards that have been connected to the System
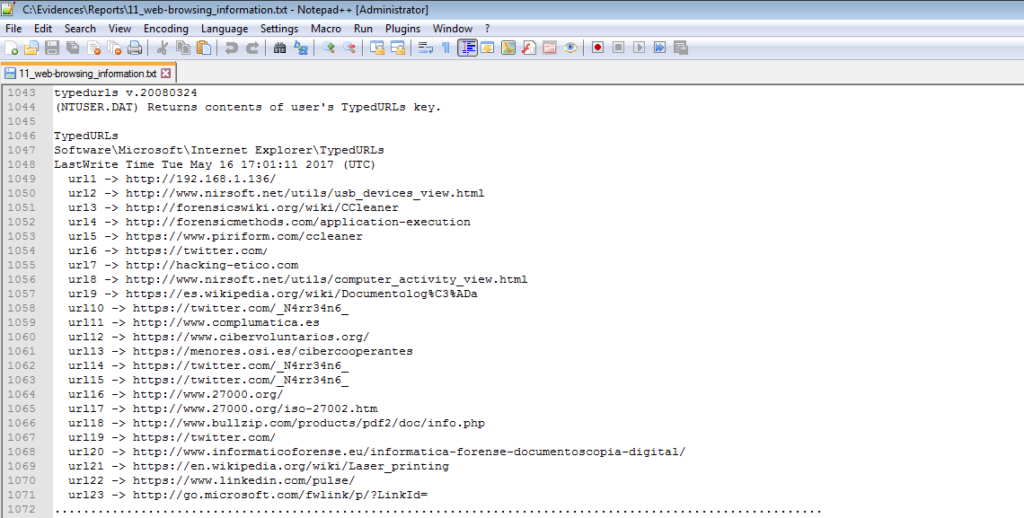
Or the web addresses that have been visited
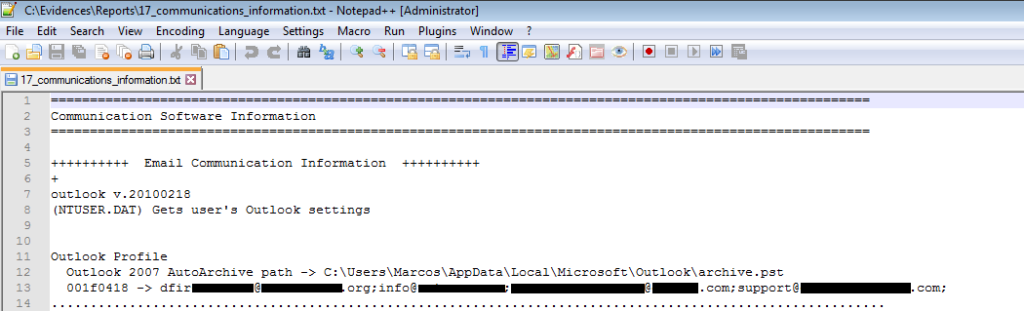
Outlook user profile data
Searches that have been made within Outlook
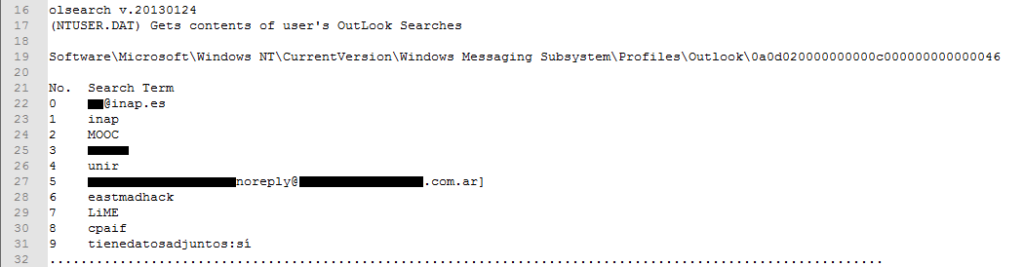
Email addresses with unread emails
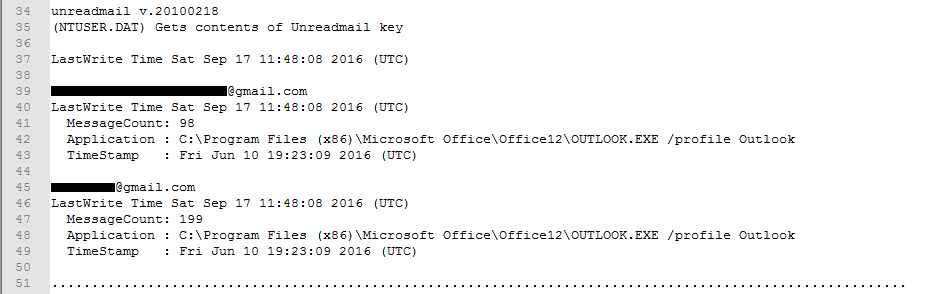
We can also be a little more courageous and examine all categories of all files of the Registry,
perl auto_rip.pl -s C:\Evidences\Acer -a C:\Evidences\Acer -n C:\Evidences\Acer -u C:\Evidences\Acer -c all -r C:\Evidences\Reports\Acer
☕️Sixth coffee☕️
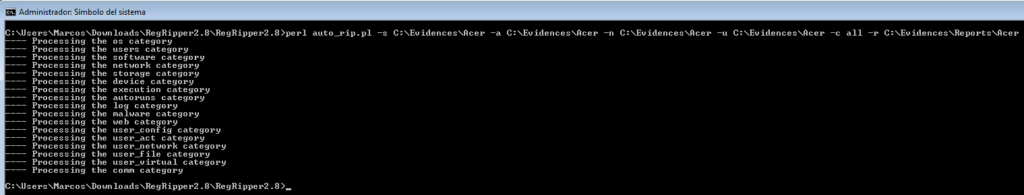
Once it is finished we will be presented with all the information extracted in a series of files, divided by categories.
Starting with the file ‘logfile’ that should be reviewed
And so we can get information on the version of the Operating System analyzed
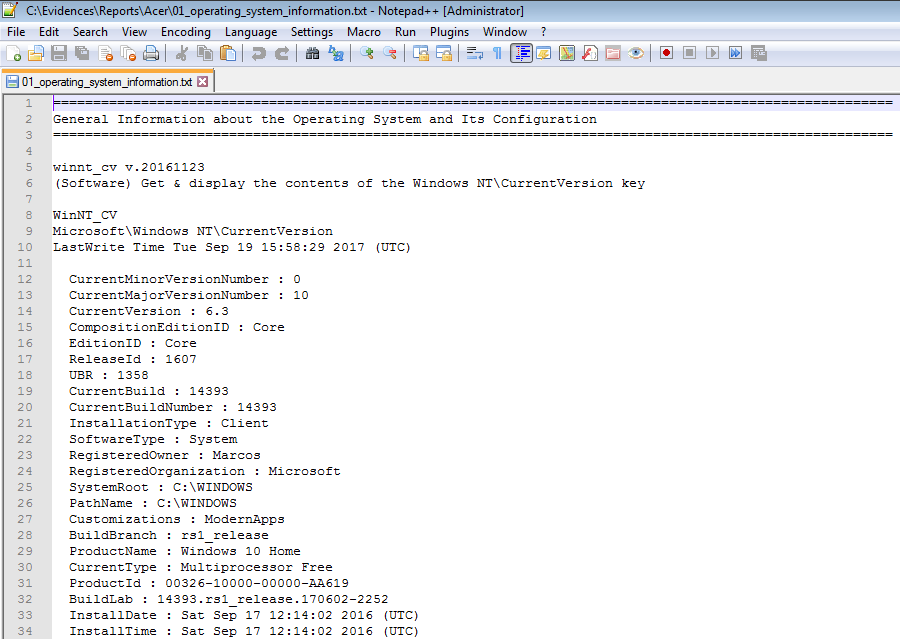
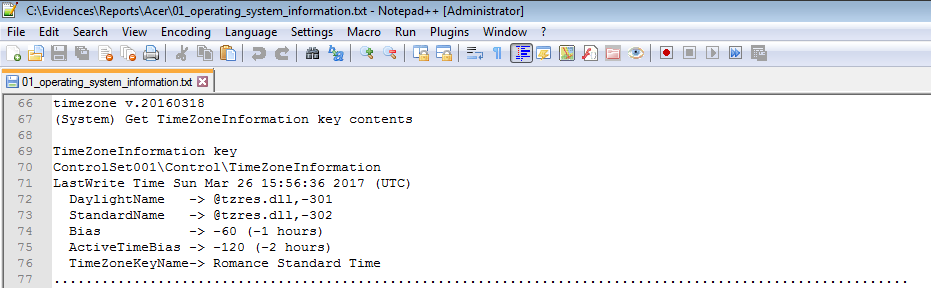
The time zone, which is an essential factor in any analysis
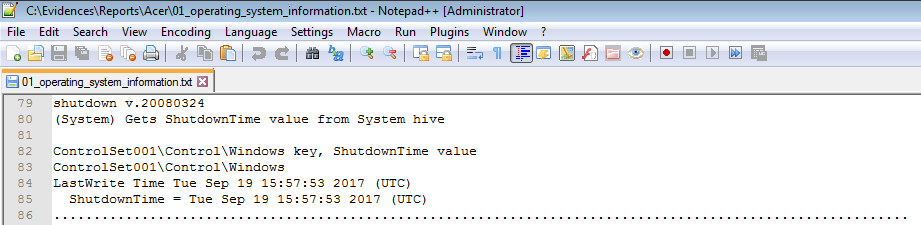
The date of the last shutdown
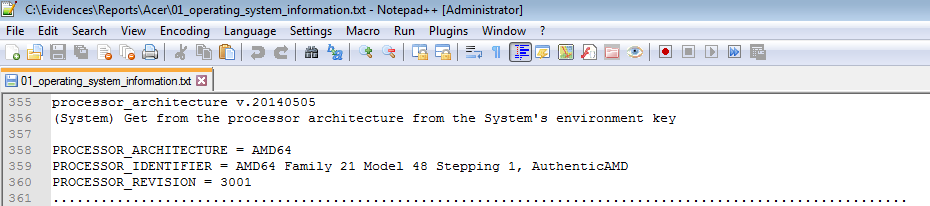
The system processor architecture analyzed
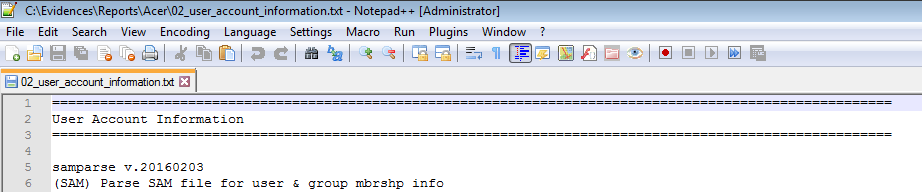
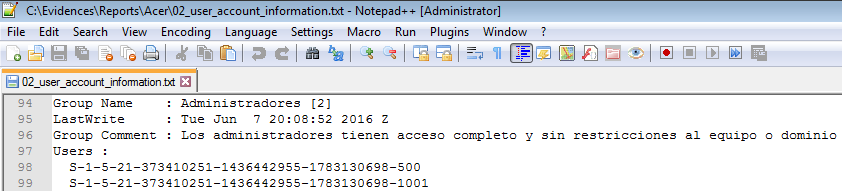
Information about the users configured in the System
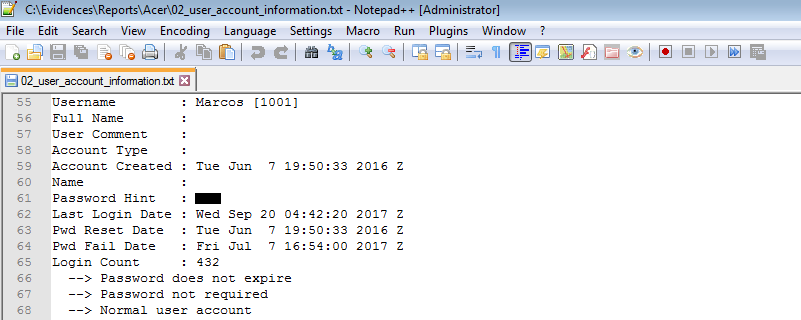
With their corresponding membership in the groups
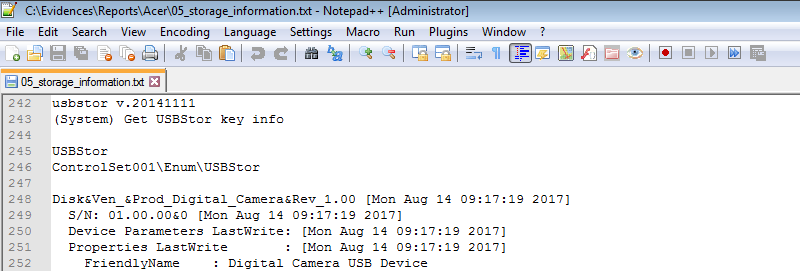
USB devices connected to the computer, with their corresponding serial number and time stamps
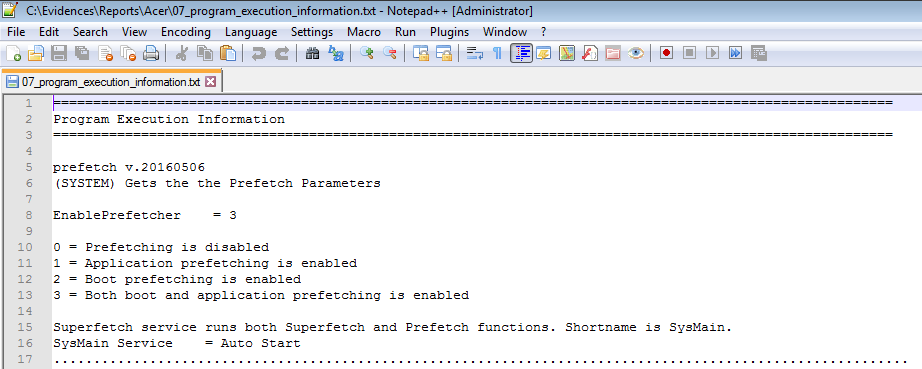
The System Prefetch setting
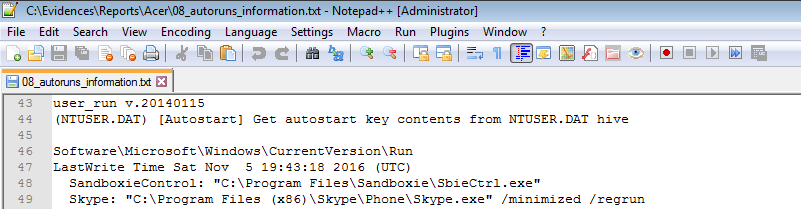
Software that runs at user logon
Configuring System Events
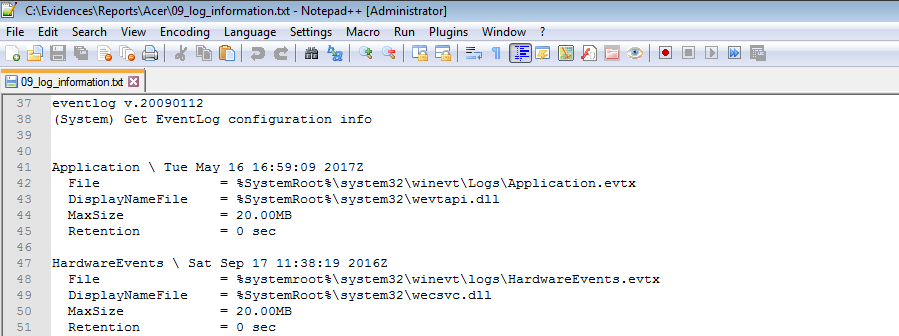
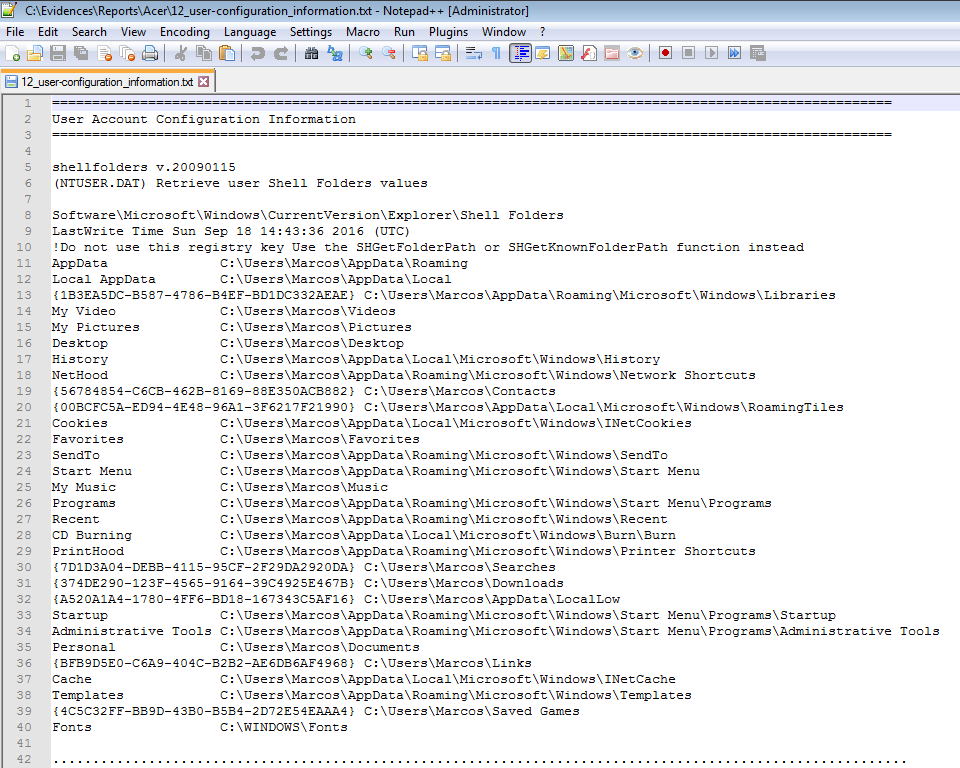
The paths to the Windows Explorer folders for the current user of the computer
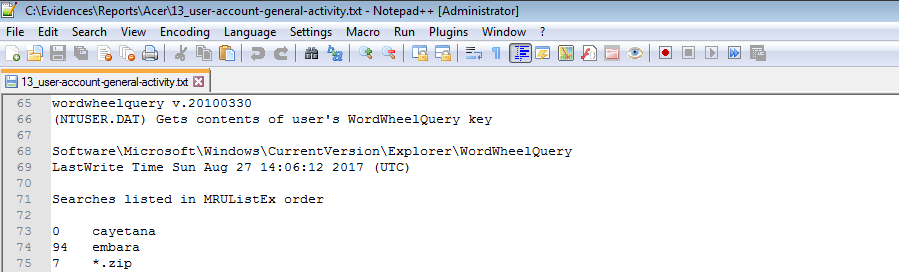
Searches that have been made in the Windows Explorer
Information about recent documents
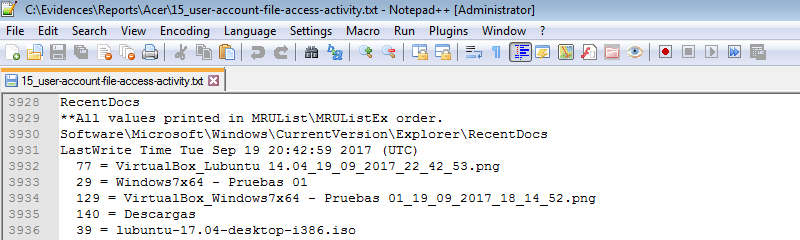
History of visited files
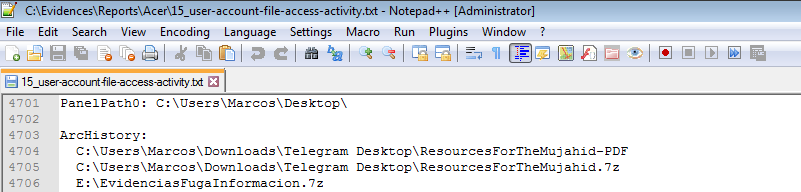
Document localization
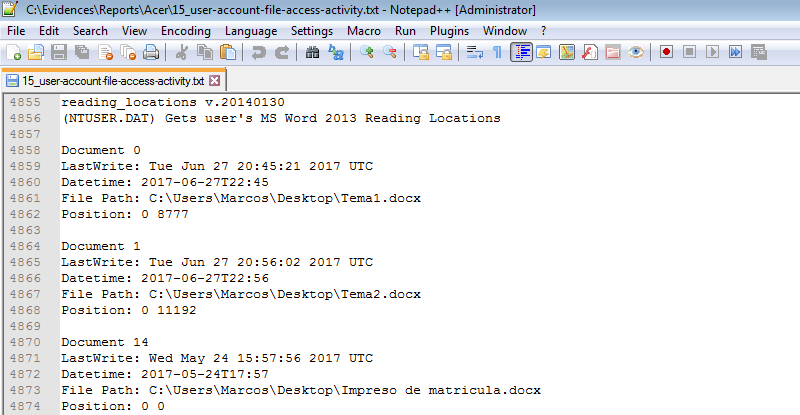
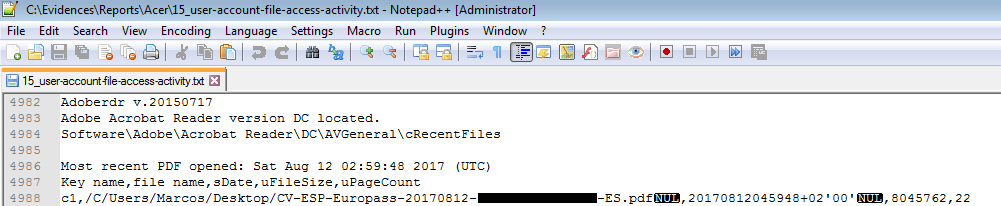
PDF documents, with their location, that have been opened
We have seen how to parse the information in the Windows Registry using several ways, exporting the results to a text file. One requirement for using Regripper plugins is to know which plugin works on each file of the Registry. For that reason it is advisable to have the list of plugins as a reference. On the other hand, most of the files will contain information, but there will be others that do not. Let’s see another way to work with RegRipper that seems really very interesting.
It is with ‘RegripperGUI‘, a tool written by Phill Moore, author of the BlogsThis Week In 4n6 and ThinkDFIR. The goal of ‘RegRipperGUI’ is, precisely, to quickly run plugins without having to search what hives they can work with, in a graphical environment. It is very simple to use.
We downloaded it from its official site in Github

We can see in the first lines of the script that it is necessary to install some requirements. As we have ActivePerl installed in our lab, we just have to call the Command Prompt and execute
ppm install dmake
ppm install Parse-Win32Registry
ppm install Win32-GUI
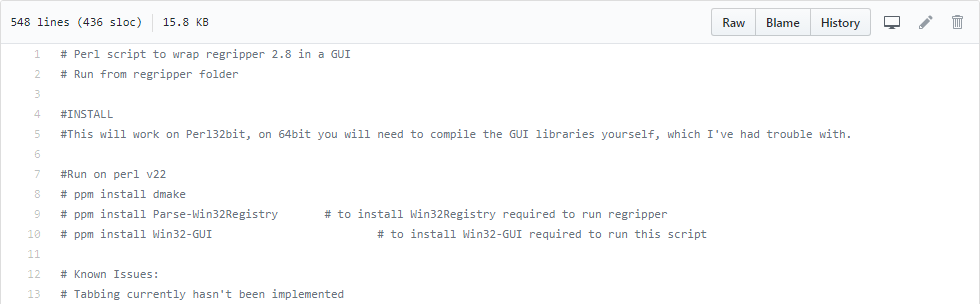
Once downloaded and uncompressed it are presented us with these two files. Copy the script ‘rr2.pl’ to the directory where we have Regripper hosted.
![]()
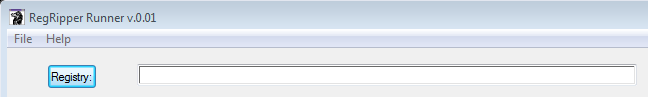
And, to run it, just you write to the terminal
perl rr2.pl
We will be presented this window
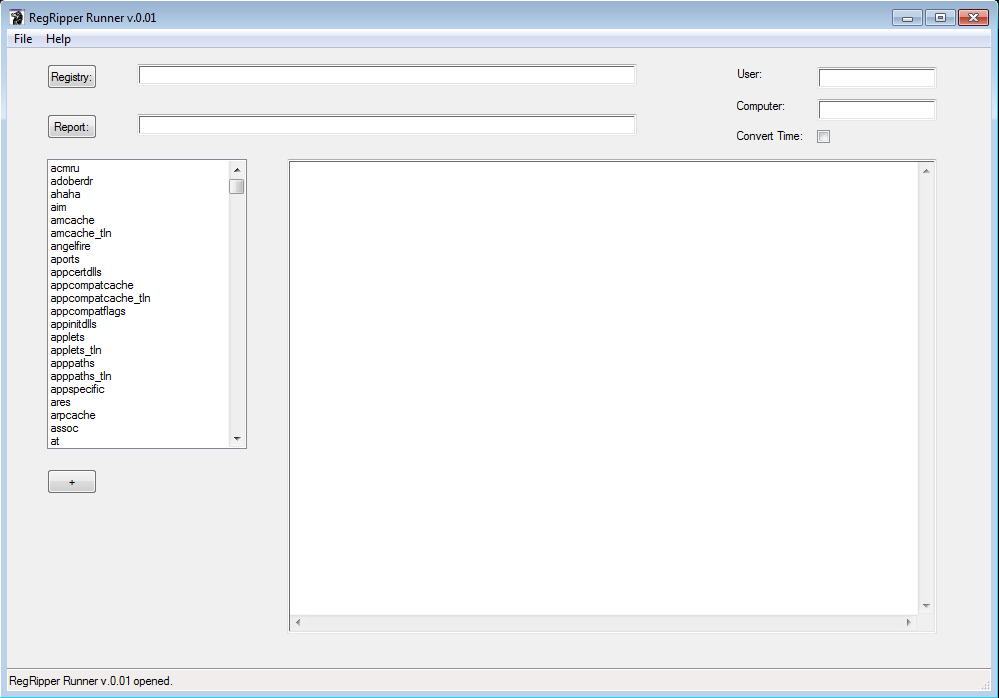
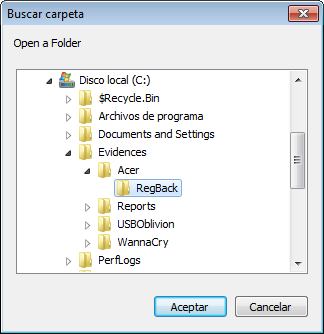
If we use the ‘Registry’ button
It will appear us a small navigation window where we will have to find the directory containing the files of the Registry that we want to parse. It will analyze all the Registers that are in that directory.
And, now, we just have to click on each plugin in the list of the text box on the left to display the extracted information.
☕️Seventh coffee☕️
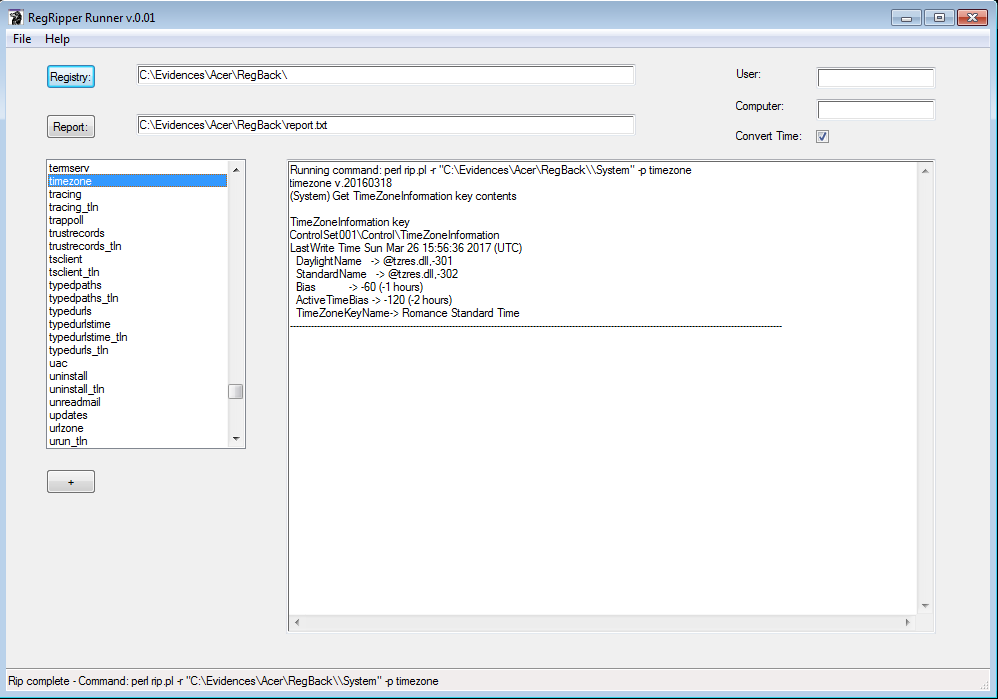
In the System console will appear the plugins that we have launched
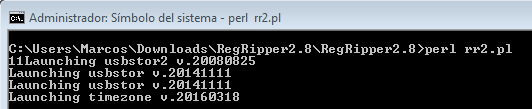
And it will inform us what command you are running with each one of them and about which registry file.
![]()
It also allows us to save a text file with the extracted information, simply by using the ‘+’ button, and it will tell us if the report was generated correctly or not
In the path that we indicated with the button ‘Report’.
If the plugin used works on several hives, and these are large, it may appear that it is not running, that our system tells us that ‘No response’. All we have to do is wait for the process to end, do not touch the System. That is, ☕️drink coffee☕️
How many coffees have you drinked? 😉
That is all, for now. See you at the next entry. This Minion, delivered and loyal to you, says goodbye… for now.
Marcos @_N4rr34n6_


4 comentarios en «Windows registry? Prepare the coffeemaker! Using #RegRipper»
Marcos ! Great blog entry 🙂
Amazing article. Thanks so much for it.
Little errata: before the «fifth coffee» you have one extra » -s C:\Evidences\Acer» in the command arguments.
Nice articles! Did you make in video ?
Los comentarios están cerrados.